Log Management Cloud
Logging is one of the responsibilities of the System Administrator (AdS). Why should you invest in a Log Management cloud solution? Ask yourself:
- How much time do I waste creating reports for internal controls and inspections?
- What is the cost of non-compliance with GDPR and Privacy regulations?
When there is a need to trace logs with a simple yet advanced system, LOGBOX is the right solution!
LOGBOX is a cloud-based log management software that allows for the processing of periodic reports and the activation of real-time alarms based on the contents of log files, effectively responding to the compliance needs of any public or private company.
Key Features
It acquires, centralizes, and archives logs
while ensuring their completeness, non-alteration, and integrity for compliance purposes
It constantly monitors the security
of all data processing processes, responding to the needs of System Administrators (AdS) in accordance with EU Regulation 2016/679 (GDPR)
Produces basic and detailed reports
creating the necessary documentation for any periodic verification and control
It allows for the setting of real-time alarms
based on log content to identify system anomalies and data access issues
It saves time and resources for personnel
thanks to the availability of a wide library of easy-to-create and interpret reports
It reduces hardware infrastructure costs
because it is an as-a-service subscription solution that is simple and scalable according to your needs.
What it allows you to do
LOGBOX is an Italian cloud-based log management software that has three main functionalities:
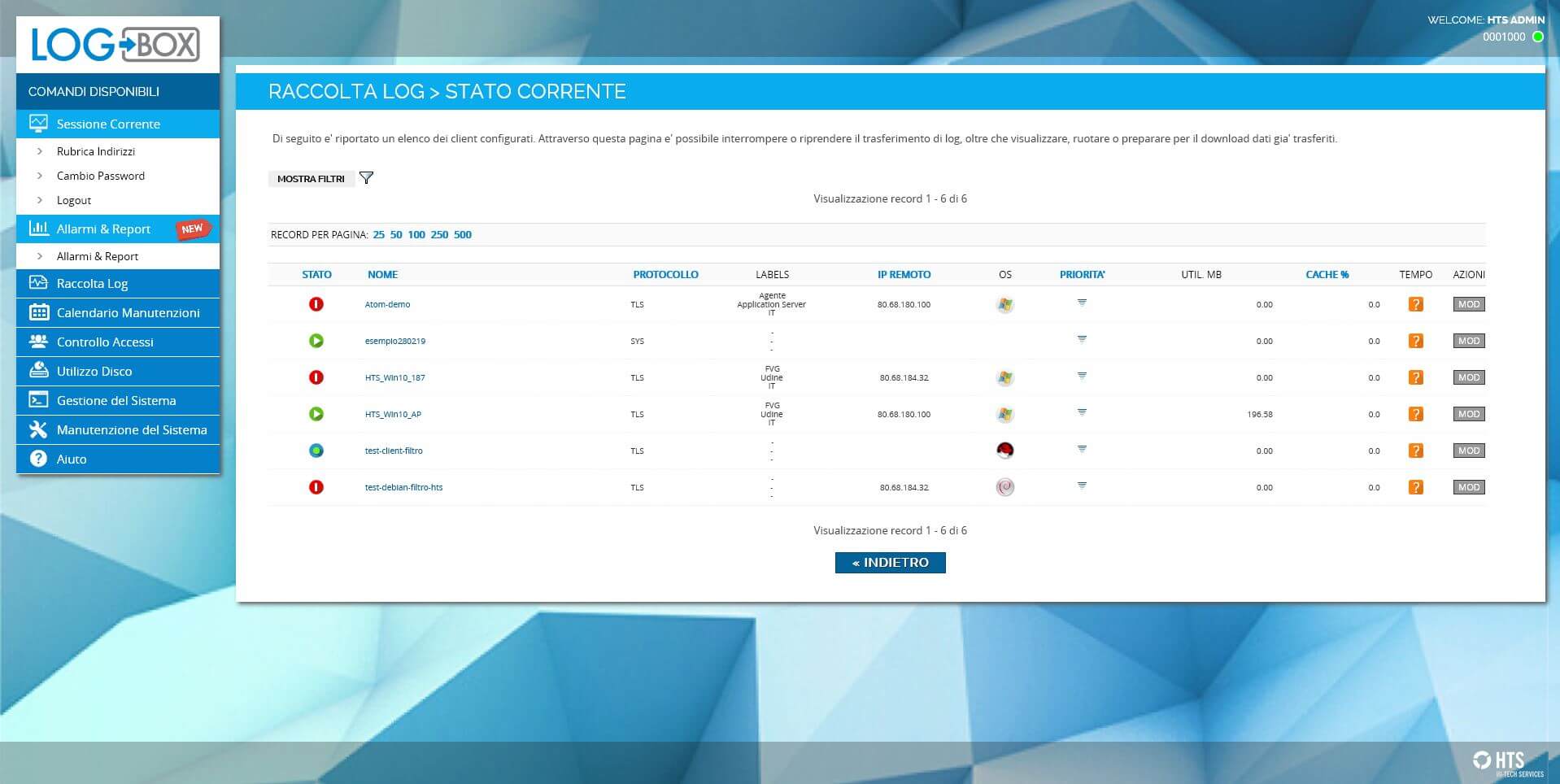
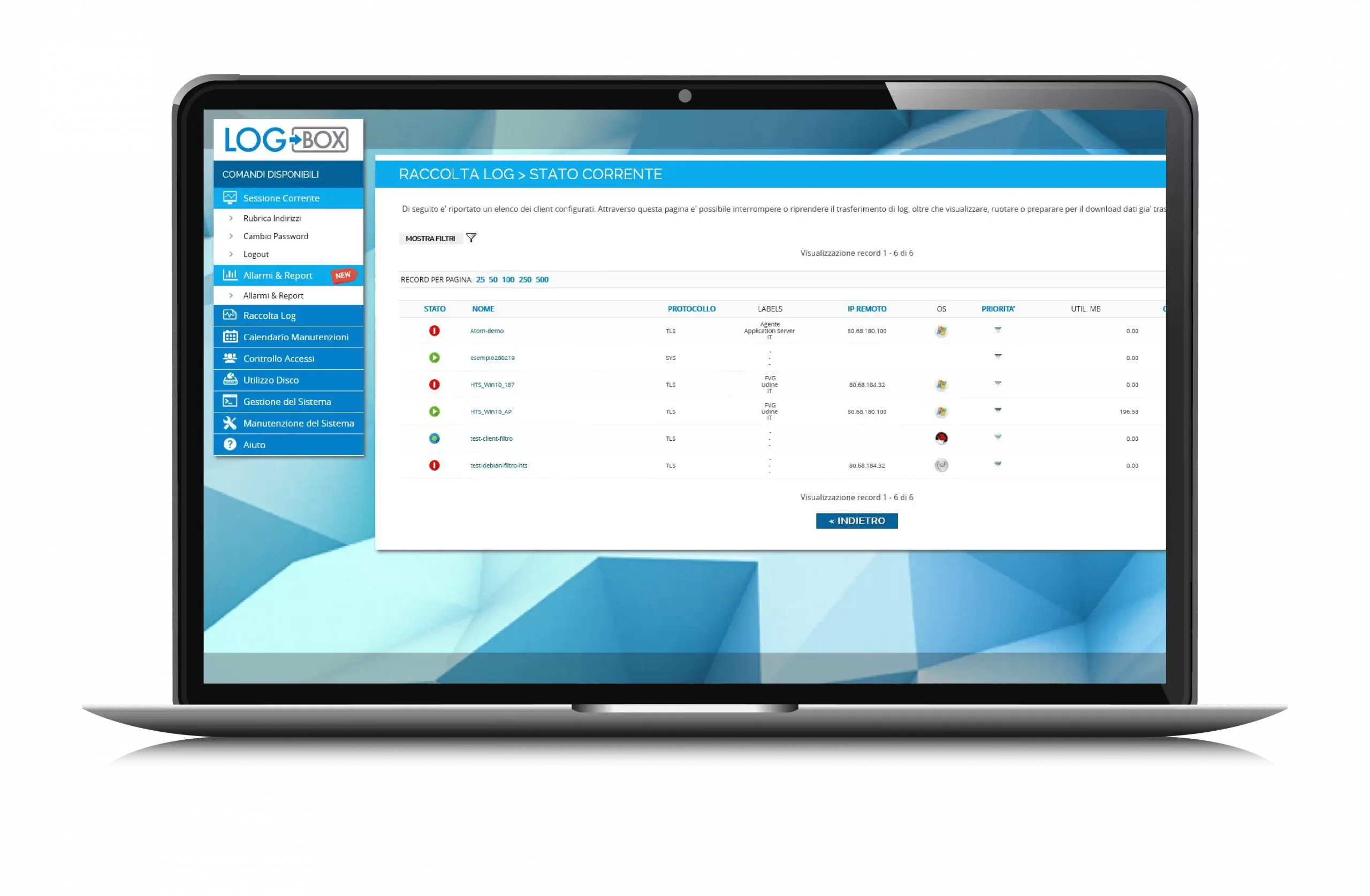
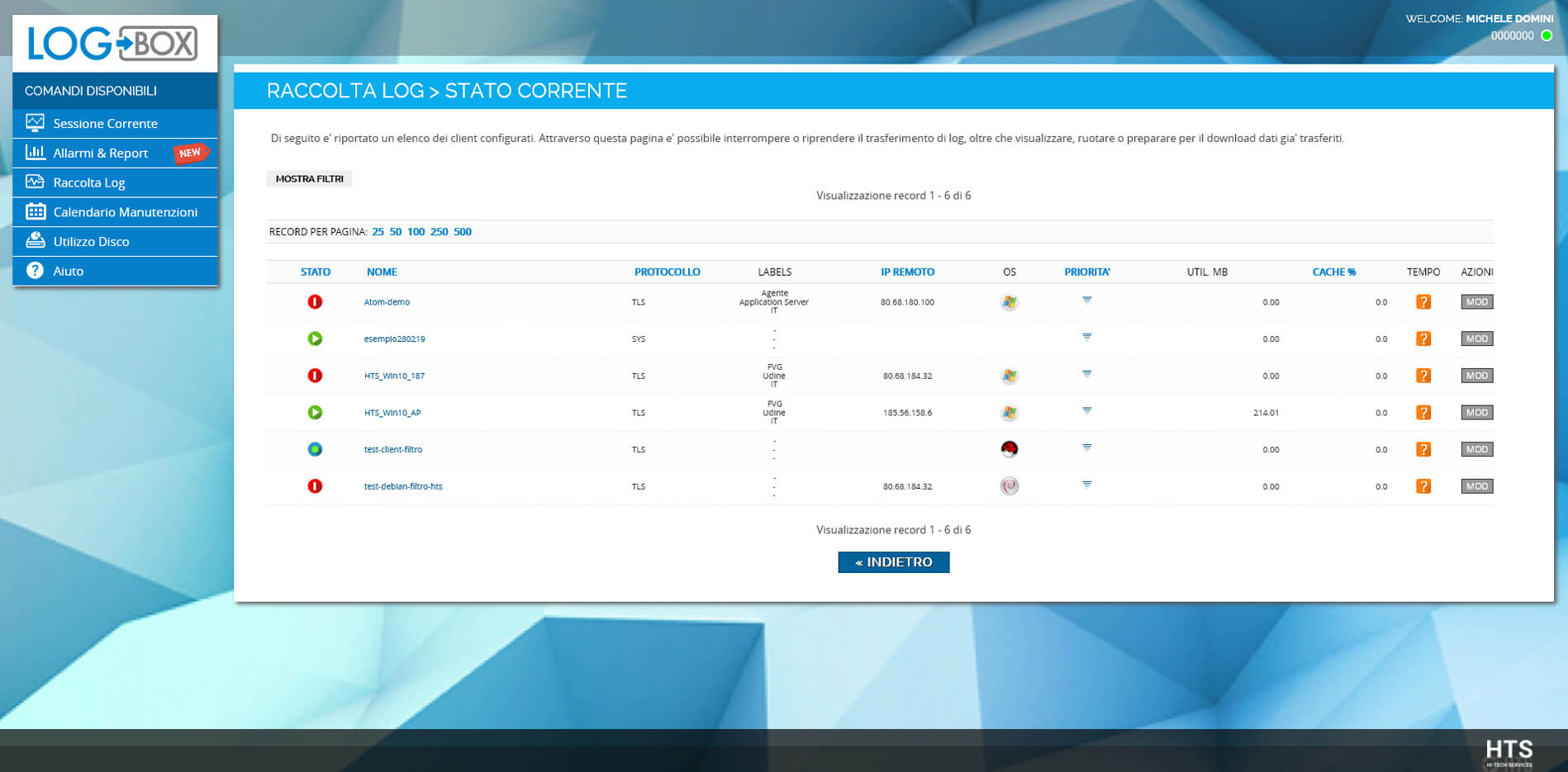
COLLECTOR
- Real-time log acquisition with agent or agentless
- Centralized configuration and monitoring
- Raw log format and data security (transport, storage, etc.)
- Automatic log deletion based on configurable retention and differentiation by log source
- System alarms for malfunctions
- Internal logs of operations and functioning status
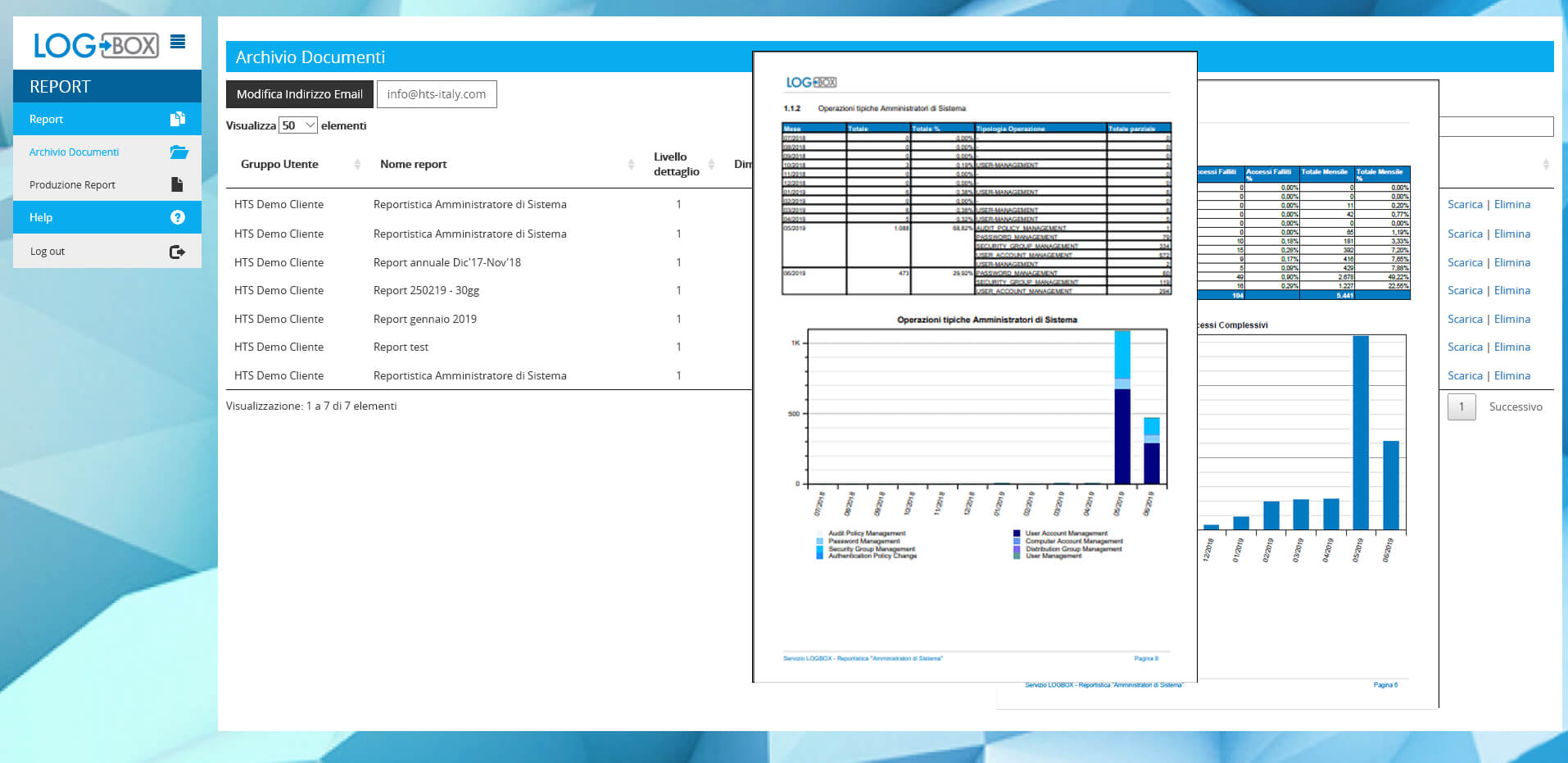
REPORT
- Independent report management
- Periodic and scheduled reports
- Wide library of standard report templates
- Custom report templates (on demand)
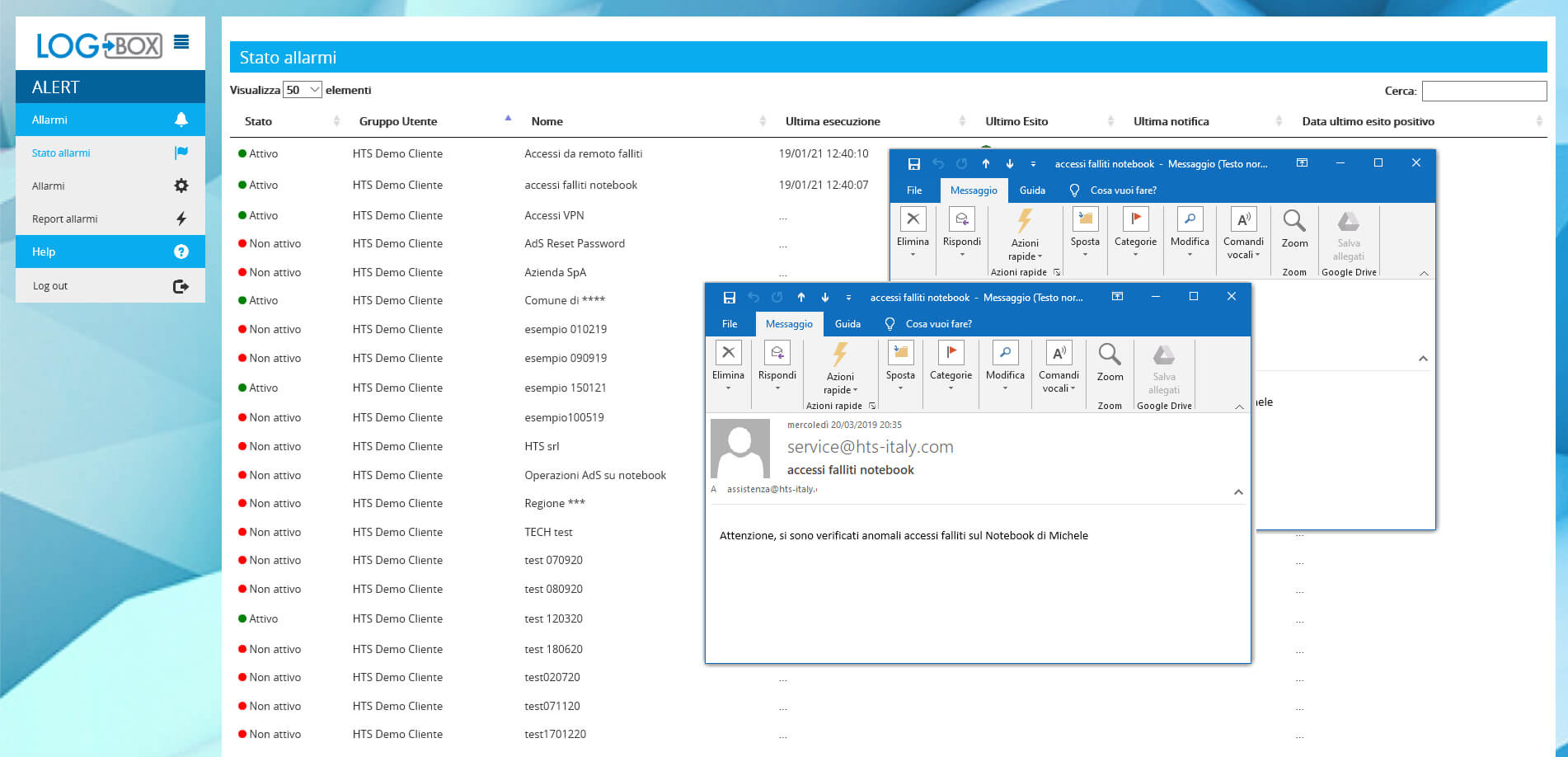
ALARMS
- Configurable alarms based on log content
- “Manual” and catalog alarms
- Included standard alarm catalog
- Custom alarm catalog (on demand)
- Activation/deactivation, status verification, and outcome of individual alarms from the web interface
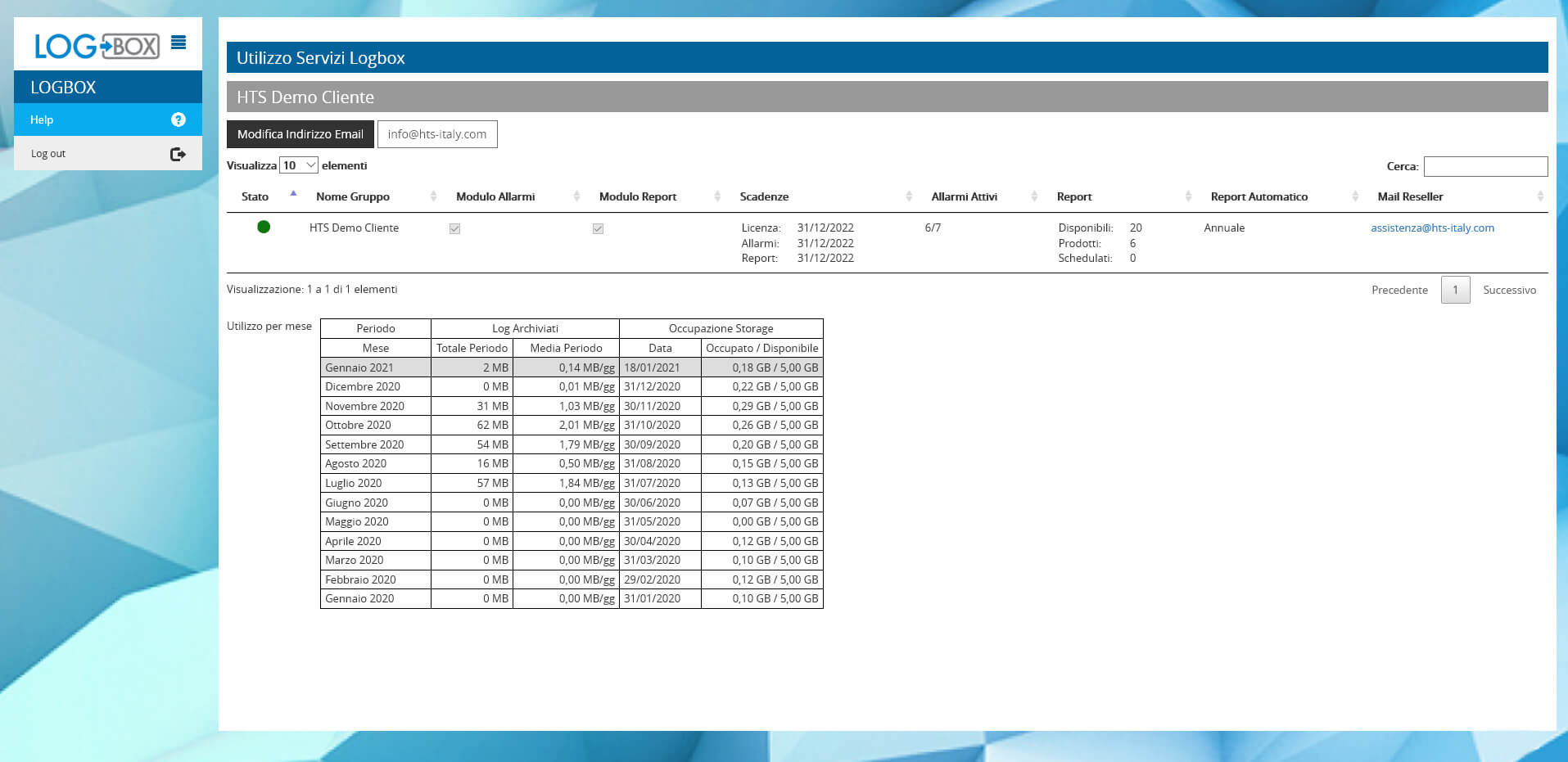
STATUS OF SERVICES
- Moduli attivi
- Scadenze canoni
- Utilizzo allarmi (attivi/disponibili)
- Utilizzo report (prodotti/disponibili)
- Occupazione storage (attuale/storico)
- Volumi log archiviati (mensili/storico)
Are you looking for an on-premises Log Management solution?
check out COALA ➔HTS also provides consulting and training services in addition to LOGBOX
HTS also provides consulting and training services in addition to LOGBOX. Through its team of certified professionals, HTS supports digital transformation projects from analyzing the existing situation to deploying the necessary tools for security and Log Management.

➔ Contact us for more information